If you’ve used my services, you know what Remote Tech Support entails. With my guidance, you’ll download or launch a program that allows me to inhabit your computer. While we talk on the phone, I get to view your screen and move your cursor around. It’s like I’m Casper the Friendly Ghost, haunting your computer in a helpful way!
But for all the good remote technicians out there, you may surprised to know that there are as many or more bad ones. Remote Tech Support scams are carried out every day, and trusting computer users like yourself are the targets. The bad guys use the same remote control tools and jargon as us good guys. It can be difficult to tell us all apart. So here I’ll try to write out a lot (too much?) information about these Remote Tech Support scams.
How These Scams Begin
Remote Tech Support scams are usually carried out over a phone conversation. But how does that phone call start?:
- A large notice appears on your computer screen unexpectedly. It claims you are being hacked or infected with many viruses. Or it may accuse you of viewing illegal adult content and could be arrested. A robot voice warning may blare out of your speakers, and you are urged to call a number immediately.
- You receive a robo-call in the middle of your day. The recording tells you that there is a problem with your computer or online account, and you should press 1 to be connected with an agent now!
- An email announces that a charge is pending for something you didn’t buy. Something like a Norton renewal, shipment of a large TV, or an expensive app from the Apple Store. And it says at the bottom that you should call the listed number at the bottom for any billing disputes.
These alerts almost always drop a big name: Microsoft, Paypal, Amazon, Apple, etc. But that big tech company didn’t contact you. You’re being lied to. The scammers are just looking to get that phone call started, by stealing and using a respected name and logo!
Worming Their Way Into Your Brain
Once a person is on an active scam phone call, the cyber criminal will get immediately to work. And their work is akin to hypnotism. They tell an urgent story, using very convincing jargon and details, in order to get your cooperation.
There are so many stories I can hardly remember them all:
- Hackers are attacking your PC right now!
- No worries, I can get you a refund for that charge.
- I see that your computer is running slowly, and I will fix it for free.
- We overcharged you in the past and would like to compensate you as an apology.
- You have not paid these back taxes and officers are coming to arrest you in less than an hour.
Some of these scams divert into what’s considered a Gift Card scam, but cyber criminals don’t need remote control of your computer for that. When the bad guy asks you to visit a website and download a program, the dangers multiply. And sometimes, the victim hardly realizes that they are entering into this, due to the stress & panic that the story has instilled in them.
Remote Control Software Installation
Again, these bad guys use the same remote control tools that all the good guys use. And they install in the same ways:
- You receive a link via email, for downloading their “helper” app. They tell you to click Yes on any prompt while the program loads.
- The scammer asks you to open Quick Support from your Windows Start Menu, and they ask for the 6-digit number on its screen.
- A bad guy tells you how to open a Run window. He then gives you a website to type in, something like www.ammyy.com or https://get.teamviewer.com .
Follow these kinds of steps, and you’ll be allowing a scammer full control over the computer. The cyber criminal will see the screen and be able to mouse around on the system.
Further Convincing Details
Once inside the computer, the bad guys add more details, to further convince you. They may open complicated Windows Control Panels to show you the thousands of errors on your system. Or launch a DOS window that is covered in IP addresses of the hackers targeting you. Whatever they demonstrate at this stage, it is pure fiction. But the level of detail to these fictions is usually overwhelming and impressive. Many victims are simply stunned by what they are shown.
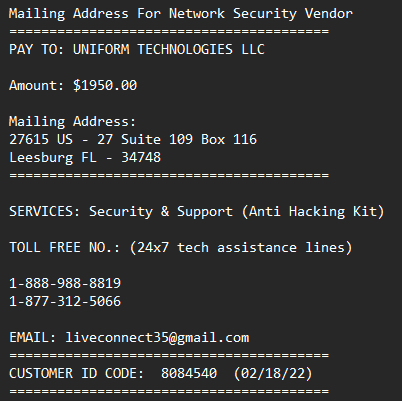
The scammer also may place specific files on the desktop or their company name on the Taskbar. A lot of them place all of their contact info in a simple text file, for you to keep:
It’s all a dog & pony show, but the more they give you to look at, the more distracted you are from realizing the truth: You have a joker in your computer, about to do something treacherous!
Step 3: Profit
If the scammer has gotten this far, they will now start the financial part of the scheme. Depending on their script, they may:
- Ask for your credit or debit card
- Tell you how to mail them a check
- Request that you open your online banking website to initiate a payment or refund
While all of these are aimed at stealing money, it’s the last one that’s the worst. When they get a victim to log in to their bank site, the bad guys may spot the logon credentials or take note of the account numbers. Remember, they can see everything that’s on-screen! And through quick action with the victim’s mouse cursor, they can move large sums of money out of the account. Sometimes they just initiate an online payment or wire transfer. Other times, they give a fake “refund” for too much money and then convince you to transfer the excess amount back to them.
In any case, this is where they steal your money as well as your sensitive financial info.
Sidenote: if a victim detects the scam at this point, and shows resistance, the scammer may add a password to the computer. This prevents the owner from getting into their system, and the scammer then demands a ransom payment for that new password! If you ever figure out that you are in the middle of a remote support scam, turn off your computer or internet before you say anything further to the scammer. This may prevent them from taking revenge on your computer.
Damage Control
Once the bad guys get someone’s money, the phone call will wrap up and they’ll let the person go. The hypnotism will fade away and the truth will dawn on the person. At this point, the victim needs to get a tourniquet on the situation:
- Disable or uninstall the remote control software used by the bad guys. If you don’t know how to do this, turn off the computer and seek legitimate computer help!
- Contact your banking institution to let them know you may have been scammed. Describe the entire process to them, and they will know what you are talking about. Really, they will have heard your story more times than they can count. Follow all of their instructions to a tee, to protect your account and seek recovery of your money.
- Change your online banking password. Change the passwords to any sites you logged into while the bad guys were connected to your system. Change as many passwords as it takes to get your peace of mind back.
Final Notes and Commentary
When I teach people about these scams, a frequent comment I hear is “Boy, how stupid do you have to be to fall for this?” Let go of that sentiment right now. Scammers can rob people, regardless of intelligence or education level. I have helped so many people recover from these crimes, and the victims are from all walks of life. Some are business owners. Others are teachers. Many have gone to college and have Dr. before their names or many letters after their names. Let’s not victim-shame or victim-blame. We should instead focus on how skilled the criminals are at their game. Some of them truly are world-class hypnotists. Recognizing them as a serious enemy is a better mindset.
Please note that these scams are perpetrated without the use of viruses or malware. There is no amount of protective software you can install to prevent this, because it is a social-engineering scam. Instead of defeating your computer’s defenses, the bad guys are overcoming your common sense. So you must bolster yourself, with both education and a healthy mistrust for the unexpected.
Big tech companies are not going to call you out of the blue with an unexpected crisis. It’s always a scam. If you still have doubts, talk to someone else before taking action. Call a friend or a computer tech or a family member. Only call phone numbers that you can trust 100%, like those printed on your billing statements or found at GetHuman.
Postscript
I snagged the screencap above from a customer computer, following a scam attempt. They wanted $1950. The involved computer was worth $600 when it was new. It’s this sort of detail that the scammers don’t want you to think about, it’s why they talk so fast and throw so many details at you. If you ever feel swept up by a fast-talker on the phone, force some kind of slow-down, or just get off the line!
And the mailing address in the scammer pic above is to a UPS Store in a strip mall. This so-called tech company is just renting a delivery address, but it sure looks impressive, before you google it, right? And anyone can secure a toll-free number. I’ve reported the scam company to the FTC, but as soon as the feds go after these villains, they’ll just set up a new mailing address and phone number.

1 thought on “Remote Tech Support Scams”